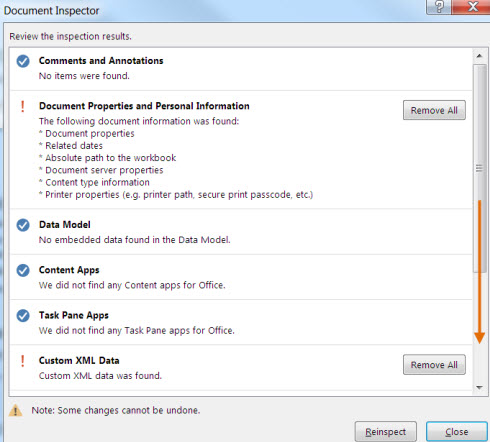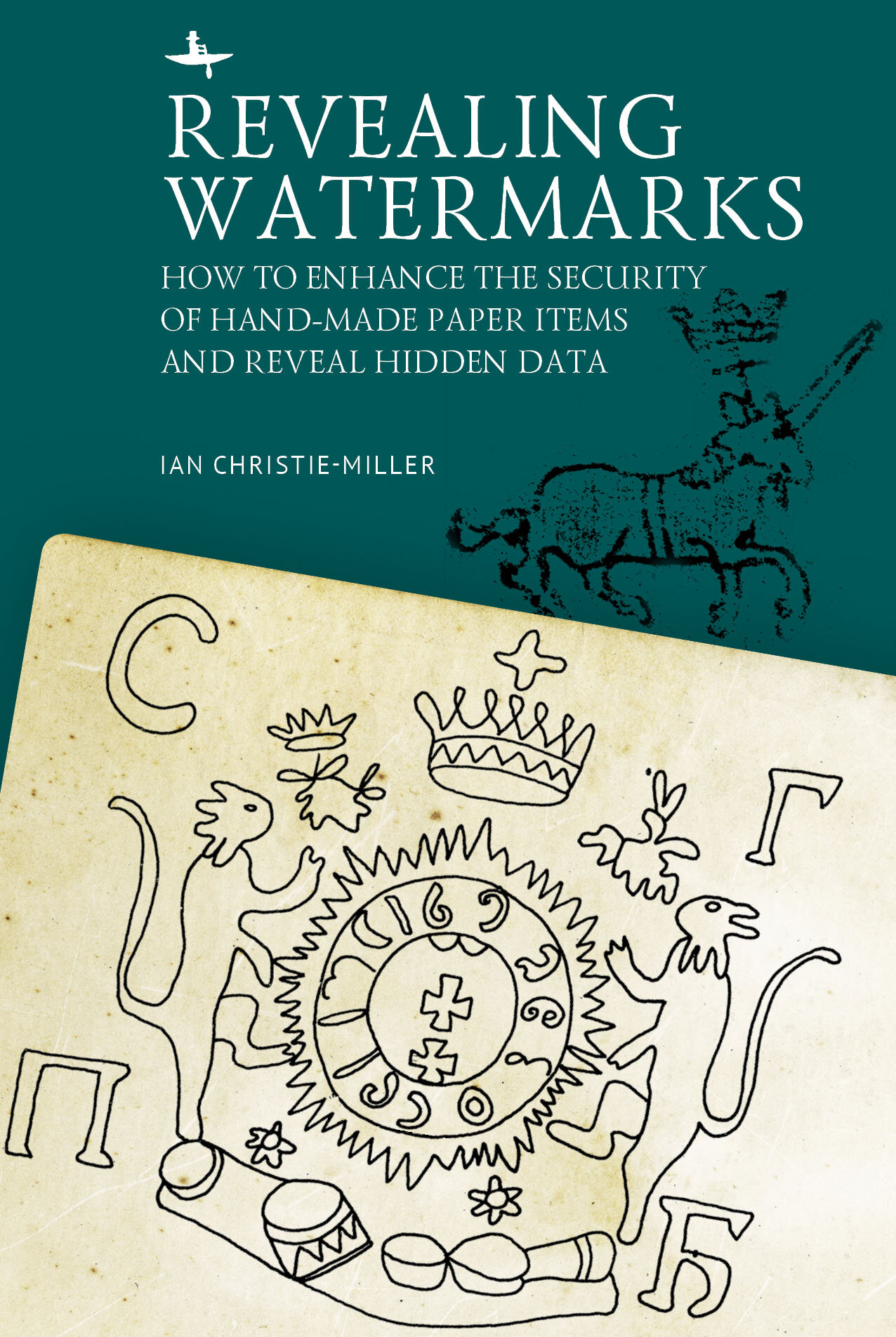
Revealing Watermarks: How to Enhance the Security of Hand-Made Paper Items and Reveal Hidden Data — Academic Studies Press
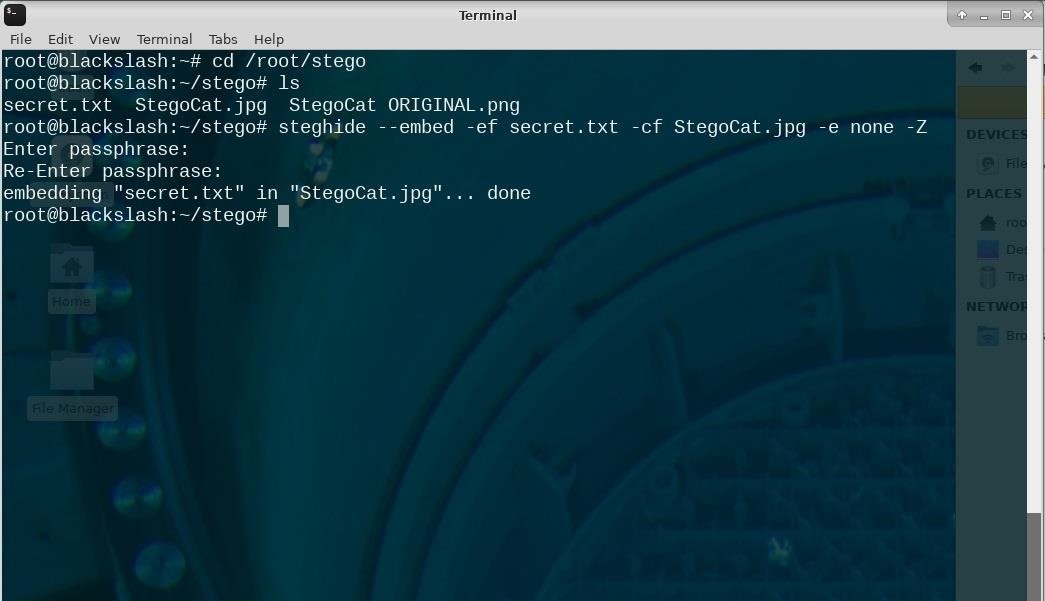
Steganography: How to Hide Secret Data Inside an Image or Audio File in Seconds « Null Byte :: WonderHowTo
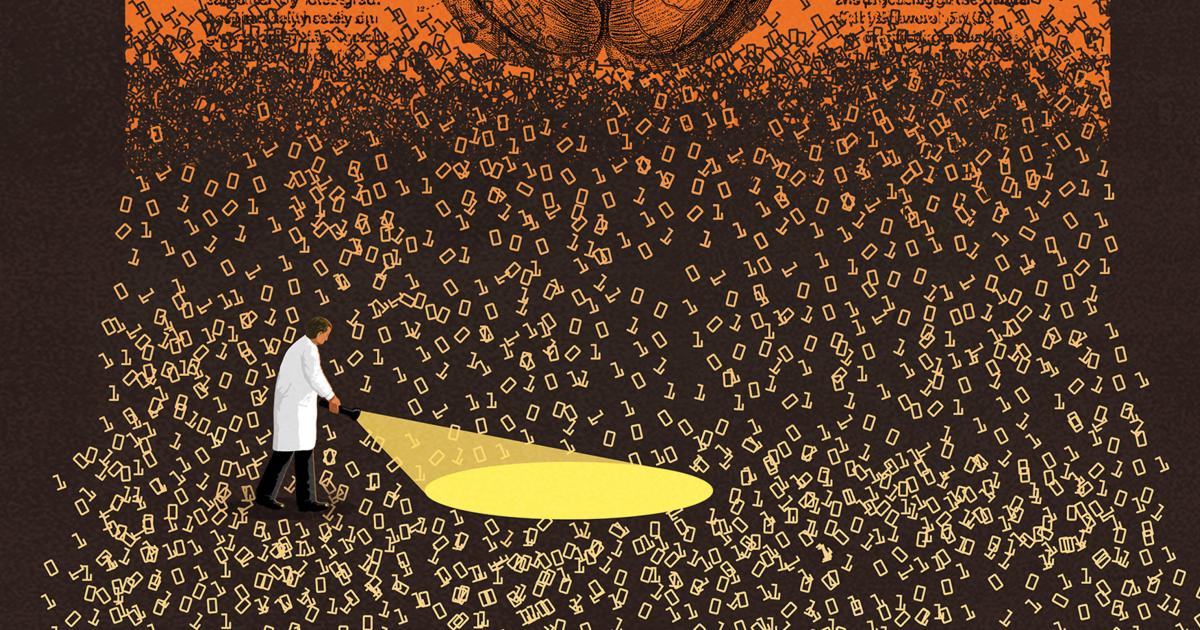
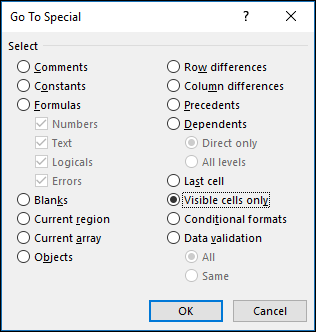
Lost Knowledge: Open Science is One Solution to Hidden Data | Hopkins Bloomberg Public Health Magazine